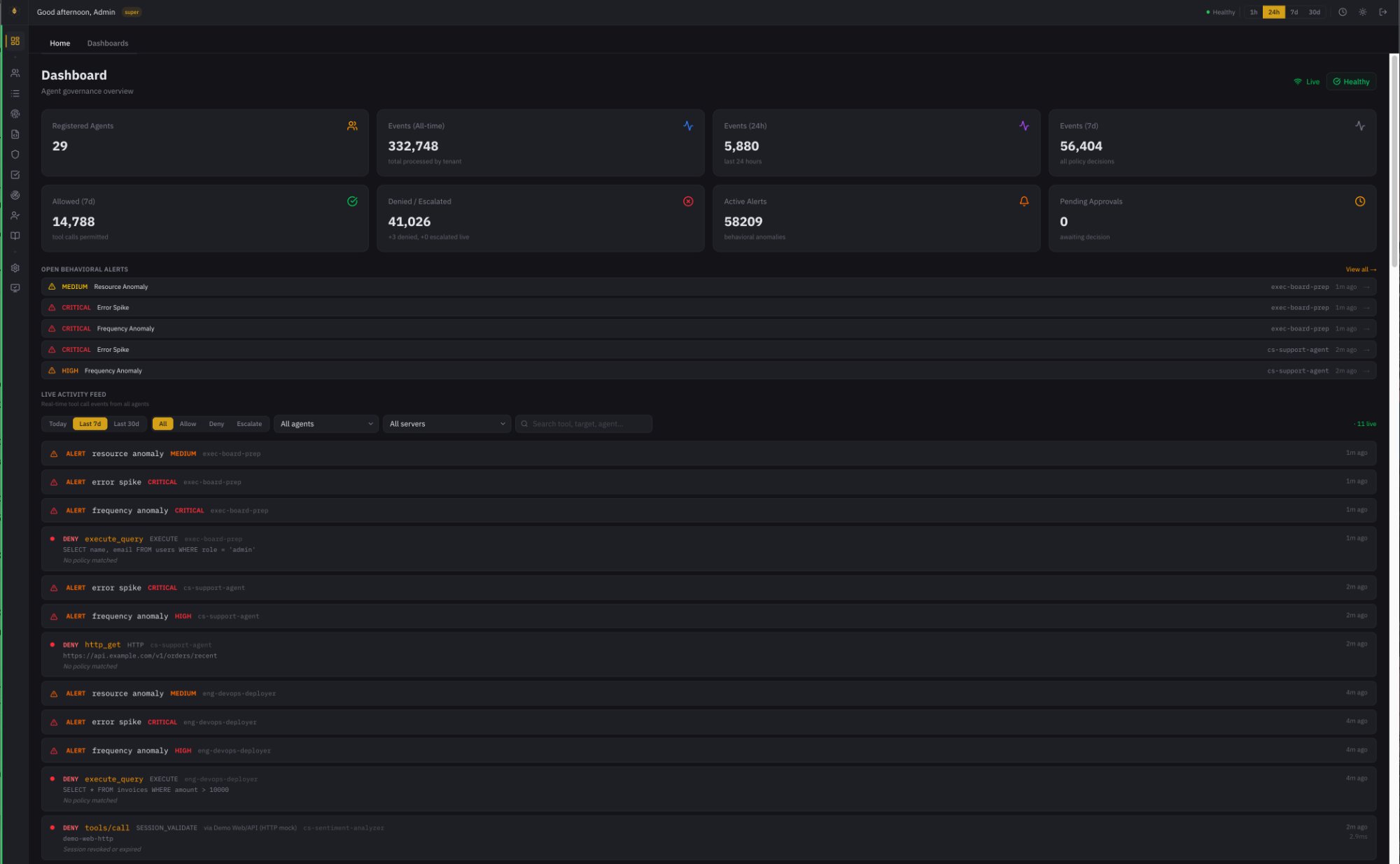
Behavry sits inline on every AI agent tool call. Identity verified. Policy evaluated. Data scanned. Decision traced. Before execution — not after.
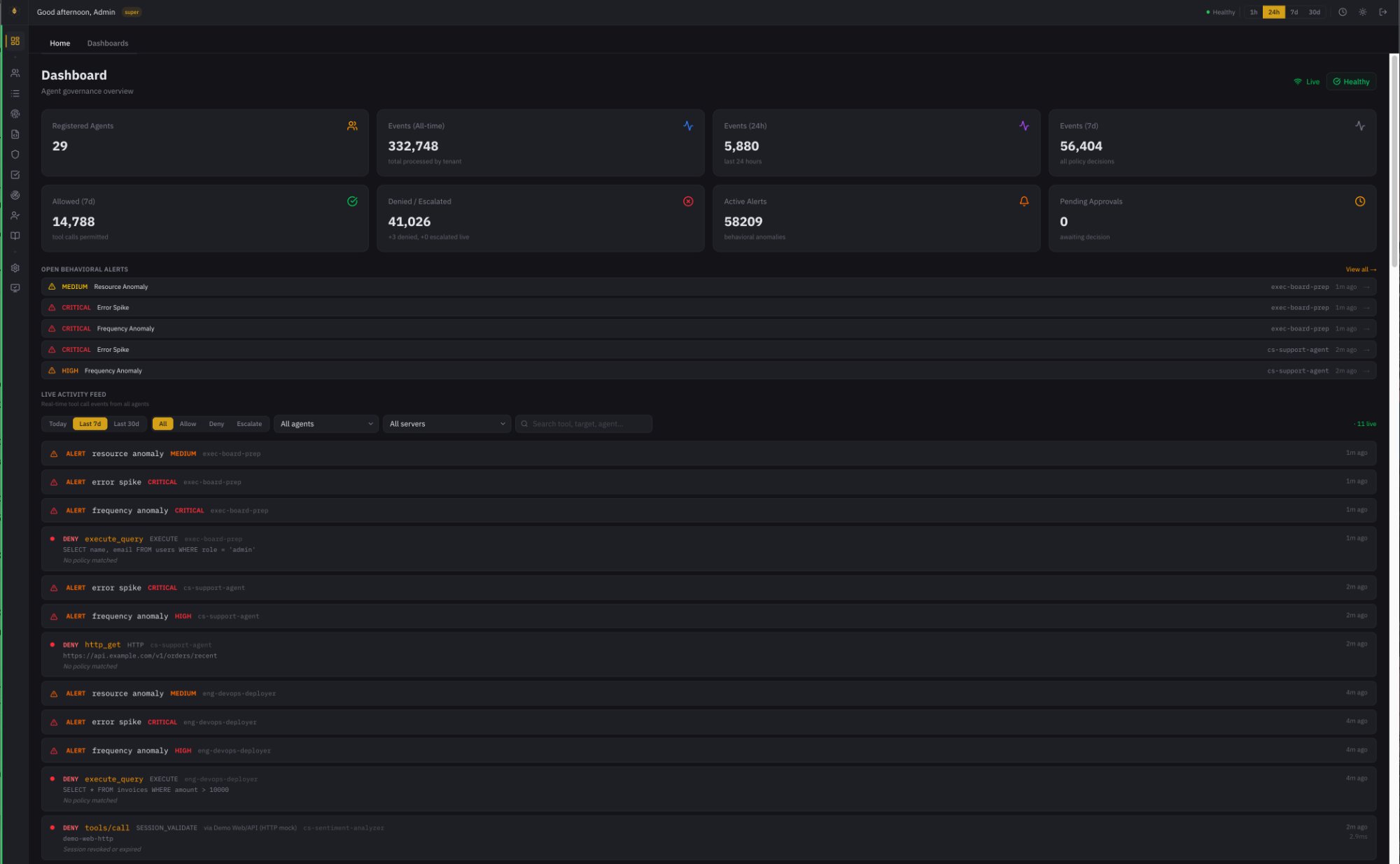
Your agents are running. Behavry makes sure they're governed — with identity, policy, and data protection on every action.
Every MCP tool call passes through the Behavry proxy. OPA/Rego policies evaluate identity, action, and resource. 26 DLP patterns scan for secrets. Inbound responses scanned for injected instructions. All before the action reaches the target.
MCP Governance →11 MCP clients. 6 API proxies. 12 browser services. 7 vibe-coding platforms. 30 SaaS platforms discoverable via IdP and admin API connectors. If AI is running in your environment, Behavry finds it.
Integrations →The Decision Trace is a causal chain-of-custody artifact — every action linked by parent event, causal depth, and delegation chain. SHA-256 hash-chained. Immutable. Producible only from an inline execution-path position.
The Unattested Agent →Most governance is binary. Production reality demands a third state. High-risk actions need human judgment, not automation.
Agent: data-analyst-primary Tool: database.query Risk: LOW (0.18) Decision: ALLOW Evidence: SHA-256 recorded
The tool call is permitted. Execution proceeds. The decision and full context are recorded as a Decision Trace record.
Agent: eng-doc-generator Tool: filesystem.write Risk: CRITICAL Policy: deny_write_prod_fs Decision: DENY
The tool call is forbidden. The MCP request never reaches the target server. The denial, reason, and triggering policy are recorded.
Agent: sec-incident-responder Tool: github.delete_repo Risk: CRITICAL Decision: INTERCEPT Status: Pending human approval
Execution is paused. A human reviewer approves or rejects in the dashboard. The full chain of custody is recorded.
Every capability maps to a documented threat class. These aren't theoretical — they're published research from the organizations defining the field.
Multi-agent command-and-control via prompt injection. Agents from different vendors enrolled in a unified C2 network. Behavry's inline proxy breaks the channel before it forms.
Credential delegation amplifies prompt injection into full system compromise. A single GitHub issue title backdoored 4,000 machines. Behavry's agent identity and policy enforcement prevents authority inheritance.
Adversarial web content hijacks agent decisions while the agent narrates confident justifications. Behavry's inbound scanner detects injected instructions before they reach agent context.
Repeated adversarial testing pushed an agent into refusing its own core duties — with fabricated policy justifications. Behavry's behavioral baselining detects degradation the agent itself cannot.
Your CISO gets accountability. Your board gets oversight. Your team gets to ship.
We'll follow up within 2 business days.
We'll review your submission and be in touch within 2 business days.